It can be difficult to collect data from hundreds of high-value OSINT data sources. It may, however, be a fairly manageable procedure if the correct tools and techniques are used.
Search Engines
Search engines are an important part of any OSINT investigation. They can help you find information on the internet about people, organizations, and other topics. There are many different search engines, but the most popular ones are Google, Yahoo, and Bing.
When you are conducting an OSINT investigation, it is important to use all of the resources at your disposal. This includes using search engines to find information on the internet. The best way to use search engines is to use a variety of different search terms to get as much information as possible.
Social Media Platforms
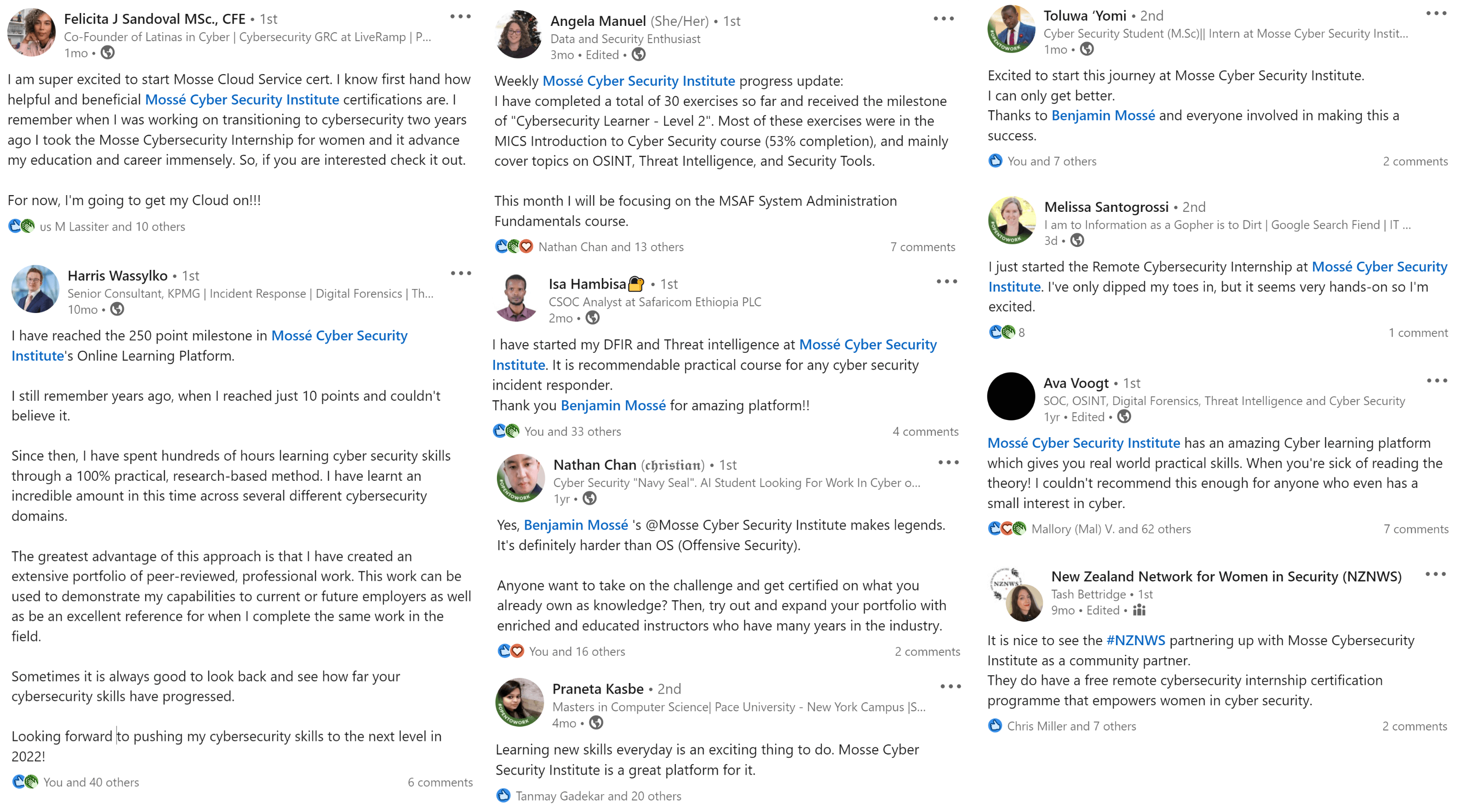
Social media platforms are valuable sources of information for open-source intelligence (OSINT) investigations. These platforms allow users to share information publicly and openly. This makes them an ideal source of information for investigators who are looking for leads or information that may not be available elsewhere.
There are a number of social media platforms that can be useful for OSINT investigations. The most popular social media platforms, such as Facebook, Twitter, and LinkedIn, are all useful for finding information. These platforms can be a valuable resource for investigators who are looking for information about people, companies, or other organizations.
Code Repositories
Some open source intelligence (OSINT) investigations rely heavily on code repositories. They can provide significant insight into a company's or organization's operations, as well as information on potential security flaws. While there are several code repositories accessible, GitHub and SourceForge are two of the most popular.
Both GitHub and SourceForge have search engines that allow you to search for specific code files or projects. They also have community forums where developers can ask questions and discuss code projects.
Email Addresses
Email addresses are one of the most important pieces of information in an OSINT investigation. They can provide a wealth of information about a person, including their name, their contact information, and their place of work. In order to find email addresses for an investigation, you can use a variety of online tools and websites.
IP Addresses
An IP address (internet protocol address) is a unique identifier assigned to devices participating in a computer network using the internet protocol. Most devices that connect to the internet are assigned a public IP address, which can be used by anyone to find and connect to the device.
When conducting OSINT investigations, it is important to understand the role of IP addresses in networking. Investigators can use public IP addresses to identify the physical location of a device and its owner. By tracing the IP address back to the hosting provider, investigators can often obtain additional information about the device and its owner, including name, email address, and contact information.
In some cases, investigators may also be able to identify the specific device model and operating system used by the owner of a public IP address. This information can be helpful in identifying the target of an investigation and understanding their online activities.
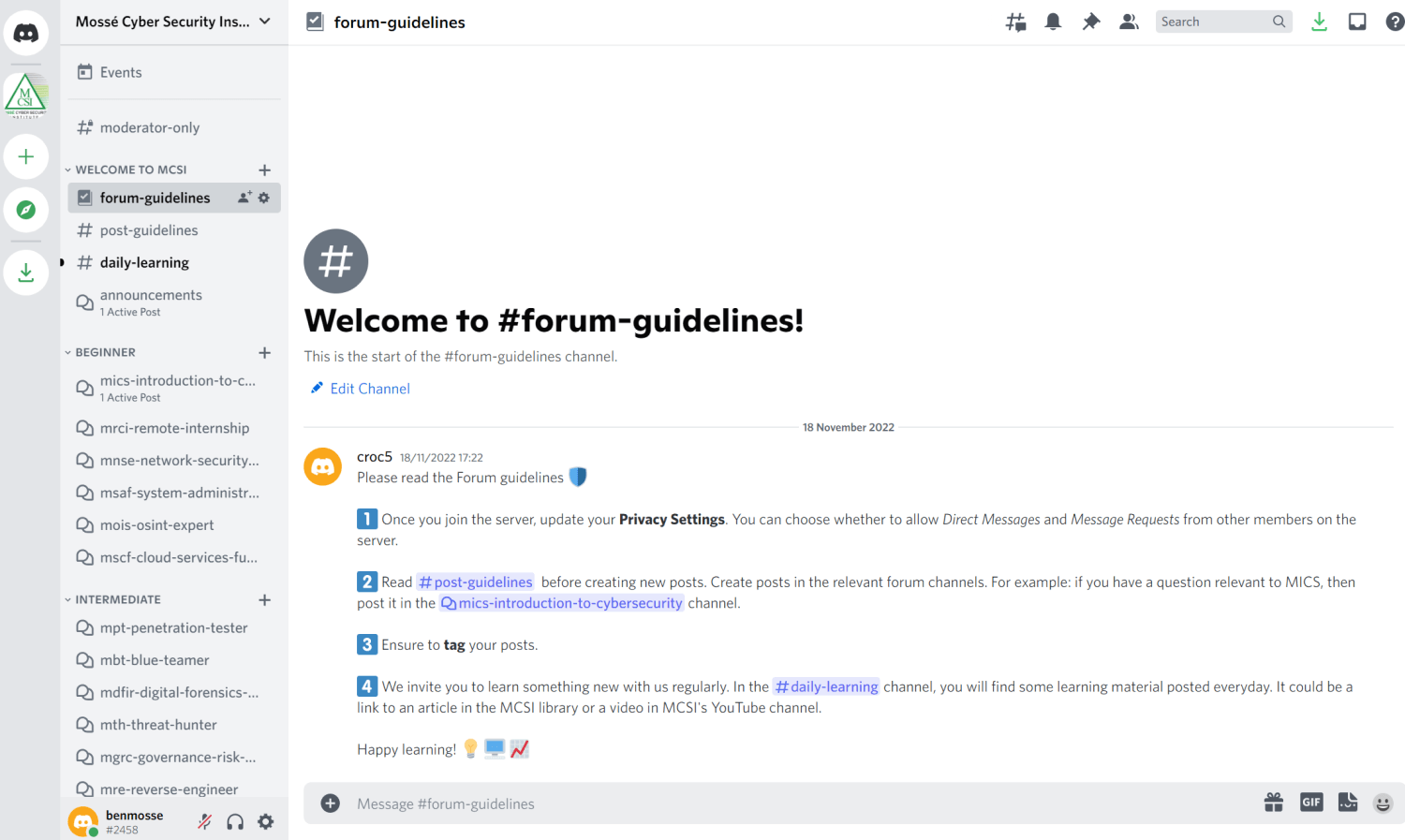
Online Communities
There are many different online communities that can be useful for OSINT investigations. Some of these communities are open to the public, while others are invitation-only.
Public communities include social media platforms like Facebook and Twitter, and online forums and discussion boards. These platforms can be used to gather information about individuals, organizations, and events. They can also be used to track sentiment and activity around specific topics.
Invitation-only communities include private social media groups, Slack channels, and email lists. These communities can be used to gather information that is not available in public forums.
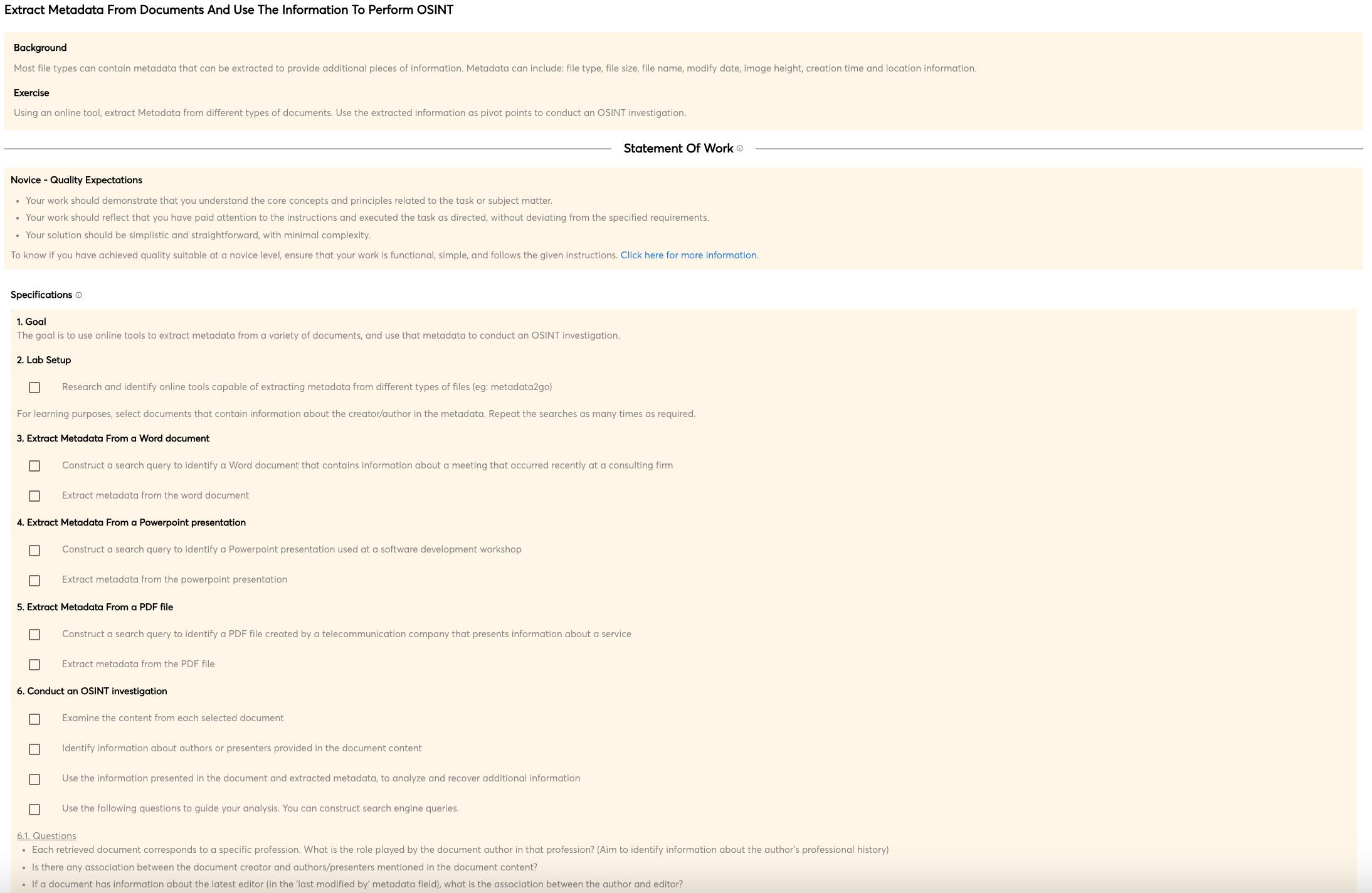
Documents
Documents are a valuable source of information for any OSINT investigation. They can provide information about the subject of the investigation, as well as their associates and activities. Documents can be obtained from a variety of sources, including public records databases, online archives, and commercial data providers.
Public records databases are a great resource for documents. They typically contain a variety of records from government agencies, such as birth certificates, marriage licenses, and property records. They also often contain court records and other government documents.
Online archives are another great source of documents. They are typically collections of historical documents that have been scanned and made available online. This can include everything from ancient manuscripts to vintage newspapers.
Commercial data providers are a great source of business records. They typically have detailed information on business owners and executives, such as addresses, phone numbers, and email addresses. They can also include information on business finances and operations.
Maps
Maps are a valuable tool for Open-source Intelligence (OSINT) investigations. They can provide a high-level view of an area or region, showing political boundaries, physical features, and points of interest. Maps can also help investigators identify relationships between people and places, and track changes over time.
Domain Names
Domain names are a valuable part of OSINT investigations, as they can provide important information about the owner of a website. Most domain names are registered through a domain name registrar, which is a company that manages the registration of domain names. By looking up the registrar for a given domain name, you can often get information about the owner of the website. Additionally, if the website is hosted on a server, you can often find information about the server by looking up the IP address associated with the domain name.
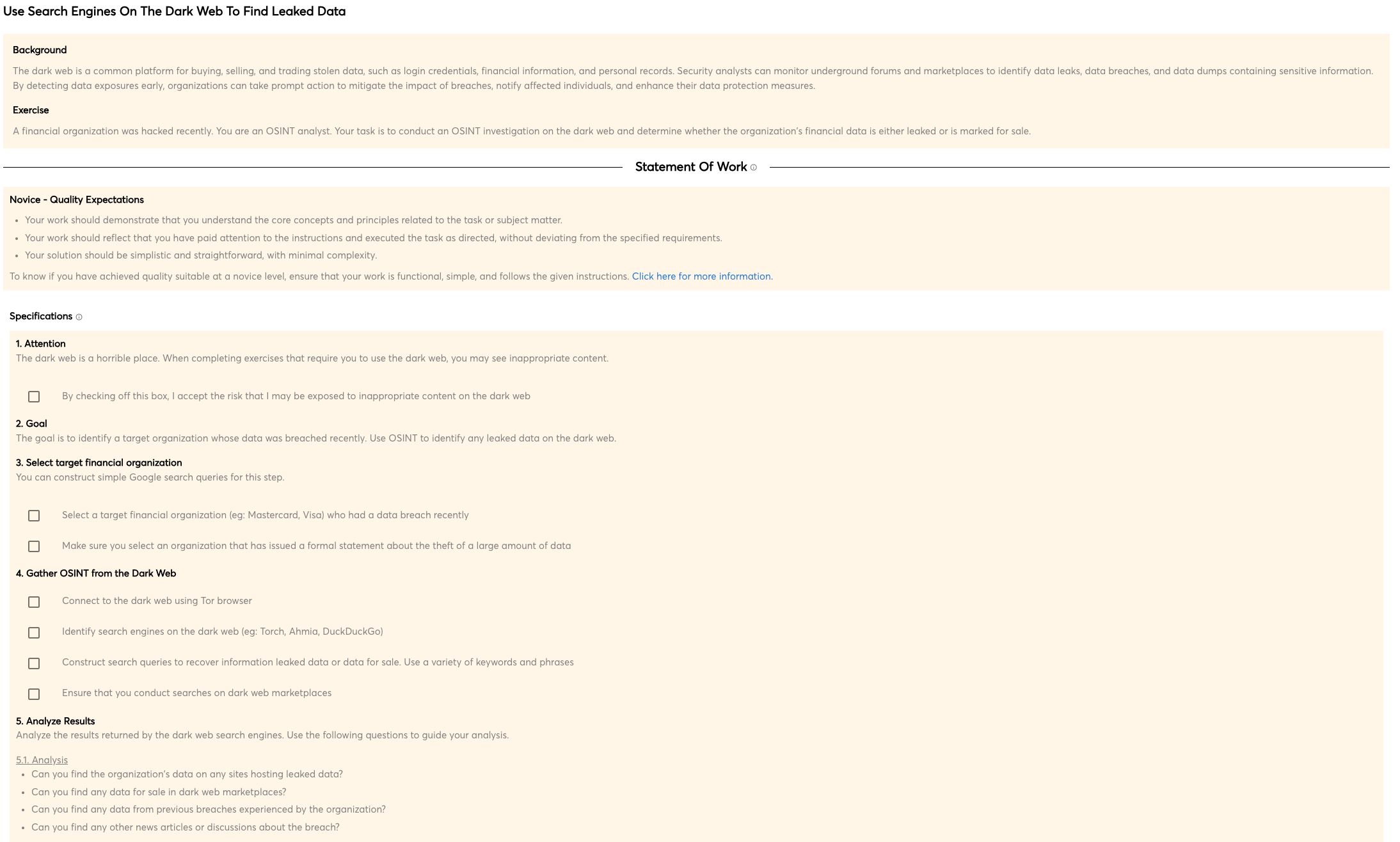
Data Breaches
A data breach is the intentional or unintentional release of confidential, sensitive, or private information. Data breaches can include email addresses, Social Security Numbers, credit card numbers, and other Personally Identifiable Information (PII).
Dark Web
The Dark Web provides a platform for anonymity and illegal activities. It can only be accessed through special software and is not indexed by traditional search engines. This makes it a haven for criminals who want to avoid detection. The Dark Web is also used in OSINT investigations to gather information about potential targets. Investigators can use special search engines to find websites and forums that are not accessible to the general public. This can give them a better understanding of the target's activities and vulnerabilities.

 Beginner
Beginner