Executive Summary
An executive summary might briefly describe the findings of a malware analysis report. The executive summary might describe what type of malware was found, how it works, and what impact it could have on a system. The executive summary might also include recommendations for mitigating the threat.
Tags and Keywords
The tags and keywords section of a malware analysis report is used to categorize the malware and its capabilities. This section is important for identifying the purpose of the malware and its potential for harm. The tags and keywords also help to determine how the malware should be handled and mitigated.
Sensitivity Classification
A malware analysis report's Sensitivity Classification section designates the confidentiality, integrity, and availability (CIA) impact of the malware. For each CIA category, the section describes how the malware could potentially exploit the system to cause harm. For instance, a piece of malware might be able to delete critical files, resulting in a loss of availability. Alternatively, it might be able to eavesdrop on sensitive communications, violating the confidentiality of the system. Finally, it might be able to tamper with data, jeopardizing the integrity of the system. By understanding the CIA impact of malware, analysts can better assess the risks posed by a given piece of malware and take steps to mitigate those risks.
Hashes
The hashes section of a malware analysis report includes the MD5, SHA-1, and CRC32 hashes of the malware sample. These hashes can be used to identify the sample and determine if it is the same as a sample that has been previously analyzed. The hashes can also be used to check for malicious content in files that have been downloaded from the Internet.
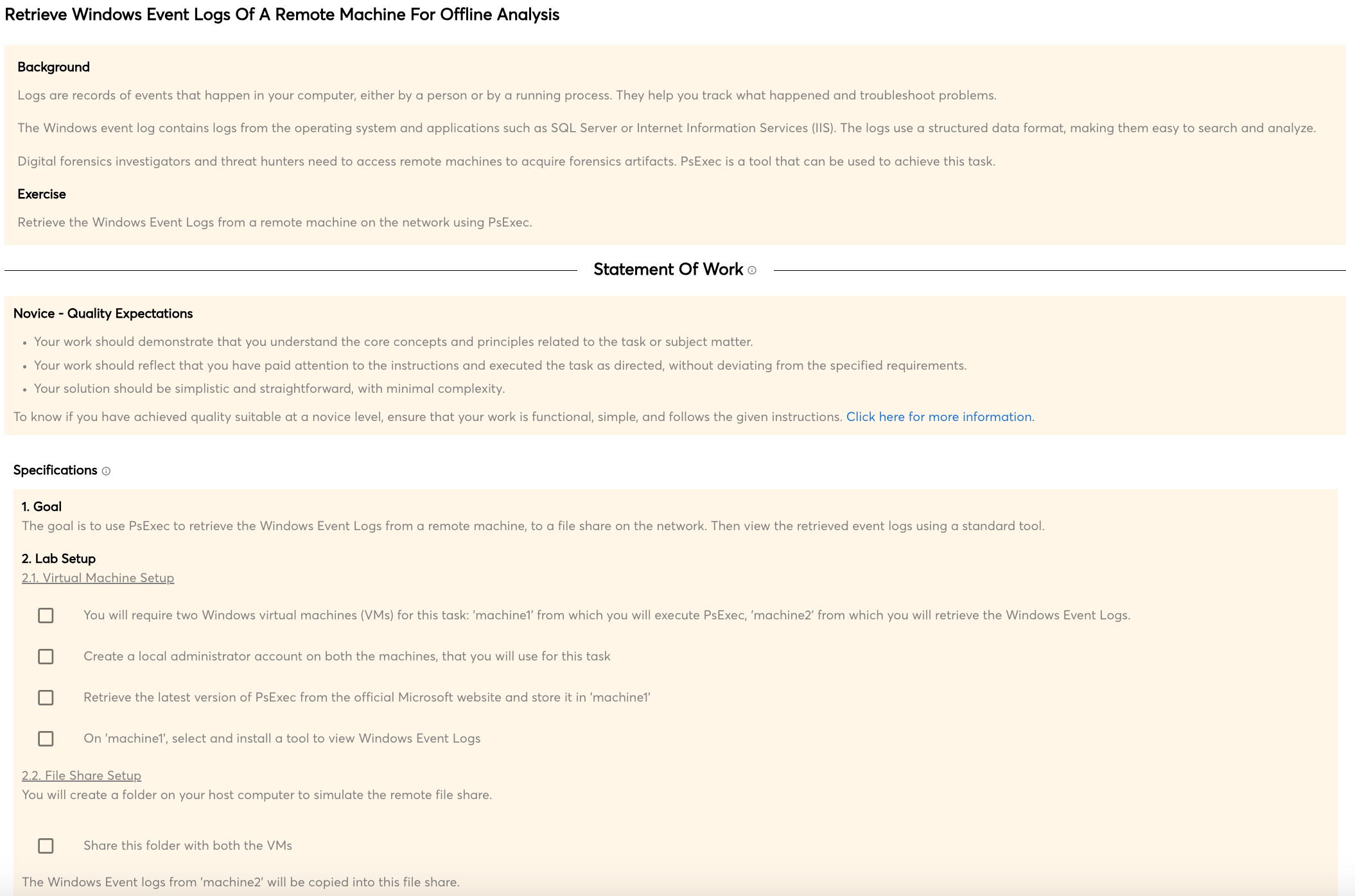
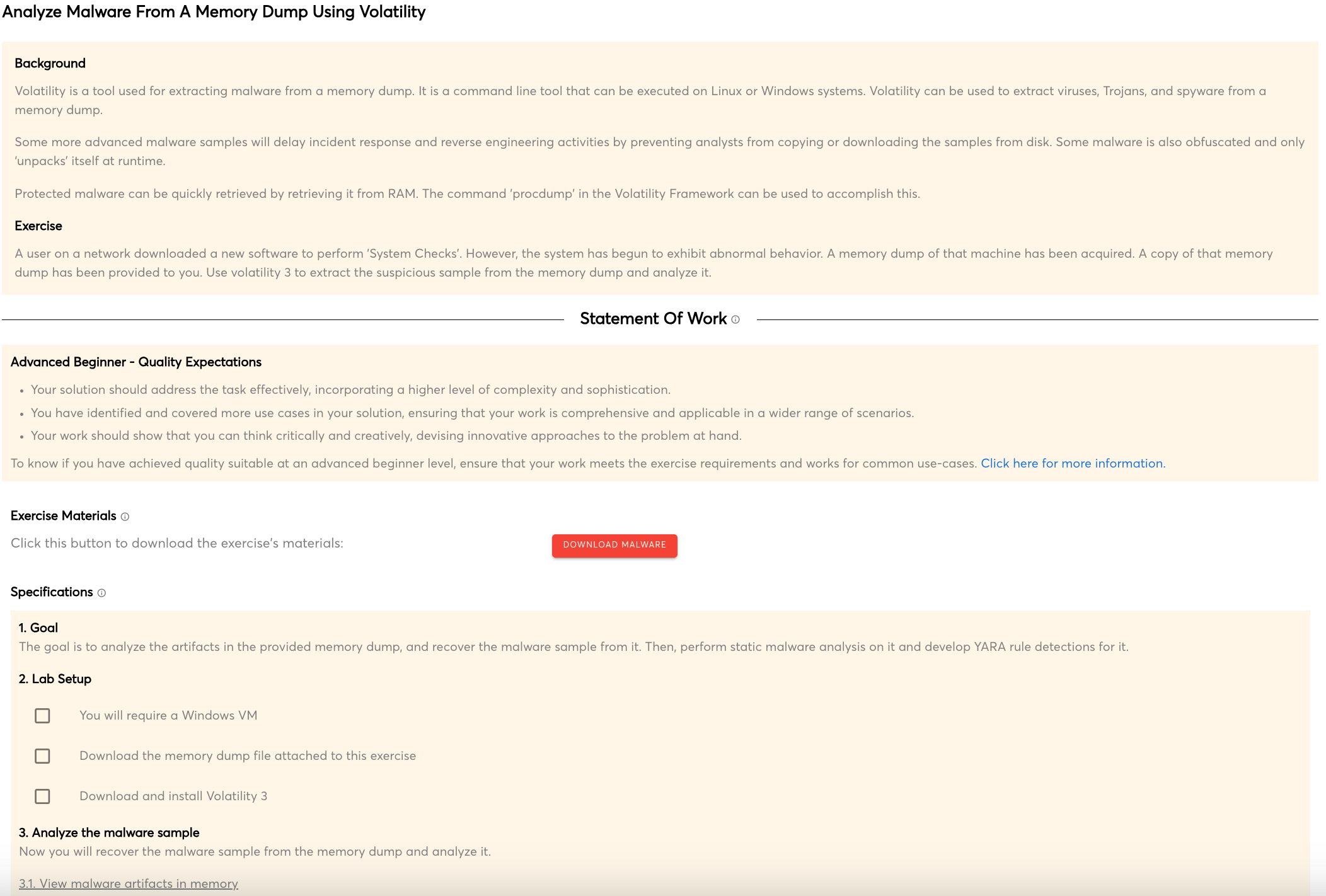
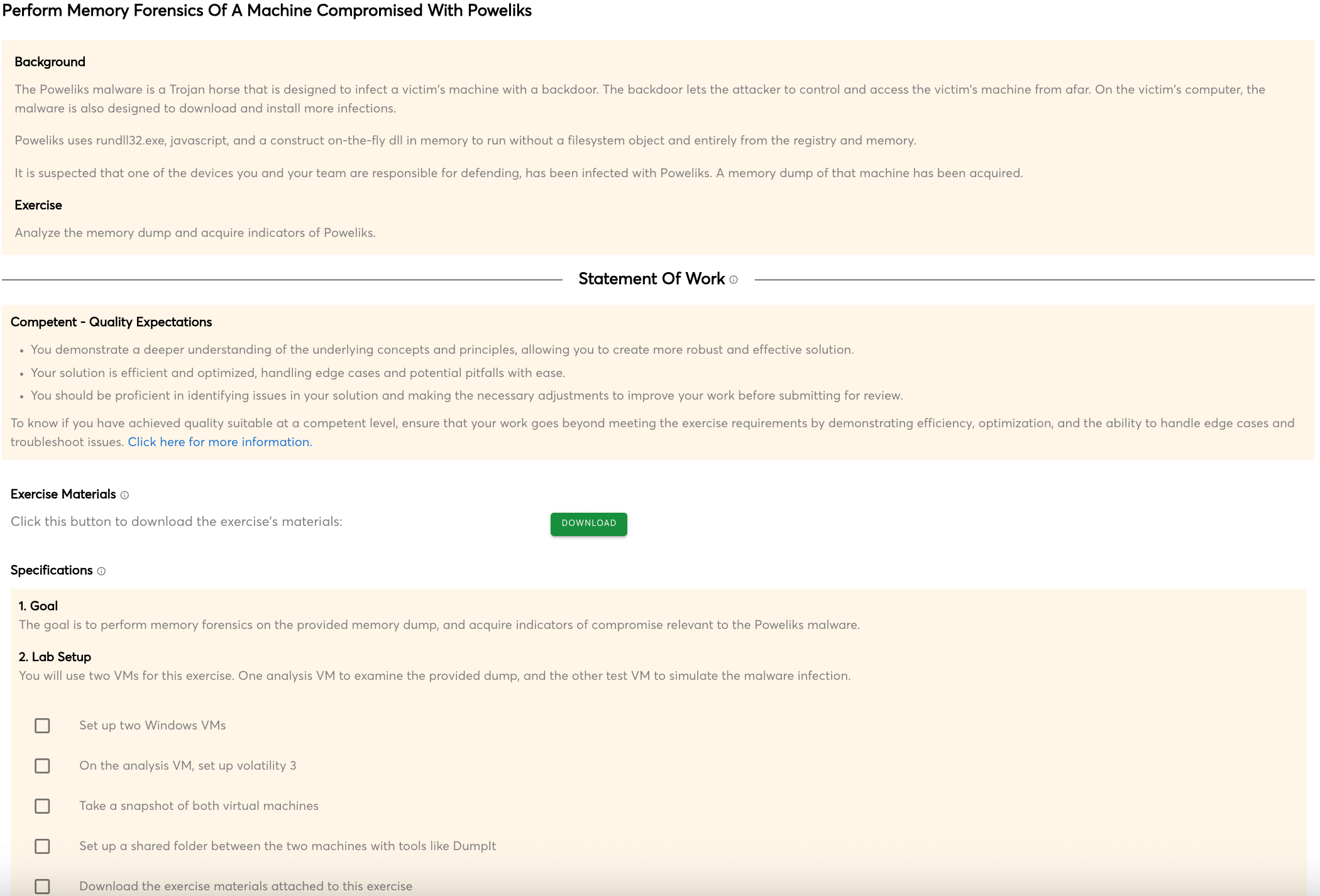
Methodology
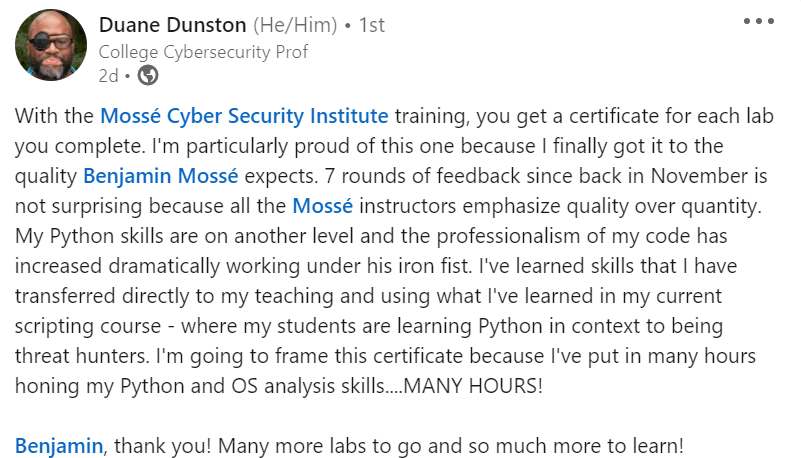
A malware analysis report's methodology section is critical for ensuring that the study is completed correctly and completely. This part should include a full account of how the analysis was carried out, including the tools utilized and the procedures used to reach the final results. This part should be presented in a clear and straightforward manner so that readers can simply follow along and comprehend the procedure.
Limitations
A malware analysis report's limitations section is used to identify any locations where the study' scope was constrained. Time constraints, restricted access to resources, or a lack of expertise of the infection can all contribute to this. It's critical to be open about any constraints in order to verify that the analysis' results are correct.
Identification and Classification of Sample(s)
Identify the type of malware that was discovered and provide information about its classification. This section includes a description of the sample, its unique identification number, and the date and time it was collected. It also includes information about the source of the sample and how it was classified.
Features
A malware analysis report should have a section that explains the features of the malware that was analyzed. This section should describe what the malware does, how it works, and what it is designed to do. This information is important for understanding how the malware works and what it is capable of doing.
Dependencies
The dependencies section of a malware analysis report lists all of the files that the malware depends on in order to run. This includes any libraries that the malware uses, as well as any other files that it needs in order to function. This information is important for understanding how the malware works, and what it would take to disable it.
Conclusions of Code Analysis and Observed Behavior
The conclusion section of a malware analysis report should provide a brief summary of your findings and recommendations. It should also state whether the malware is still active and, if so, how to remove it.

 Intermediate
Intermediate