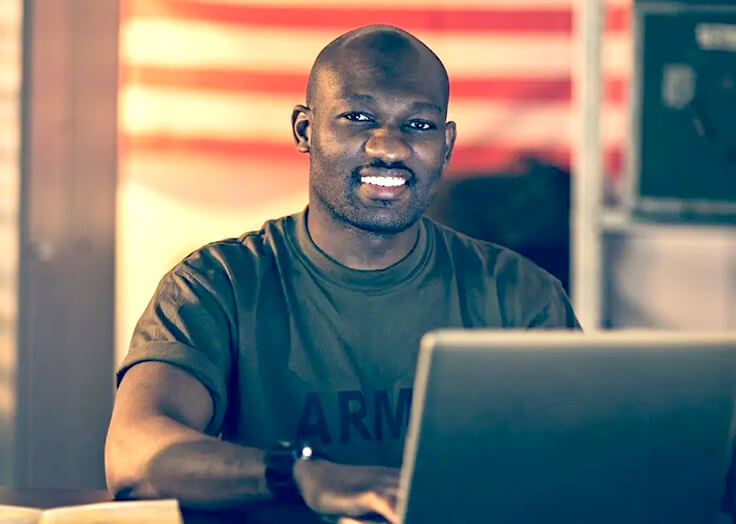
Course Overview
Learn how to leverage the power of Metasploit with our specialized bootcamp!
Dive into the dynamic world of vulnerability assessment and exploitation with Metasploit. This open-source tool is a cornerstone for security researchers, enabling them to uncover and exploit vulnerabilities in software systems. From launching attacks to generating comprehensive reports, Metasploit equips ethical hackers and penetration testers with the arsenal needed to assess security risks and identify system weaknesses before malicious actors do.
In this bootcamp, you'll delve into the intricacies of Metasploit, mastering advanced techniques for vulnerability identification and exploitation. Through hands-on exercises, you'll gain practical experience in leveraging Metasploit to launch targeted attacks, test for vulnerabilities, and generate actionable reports.
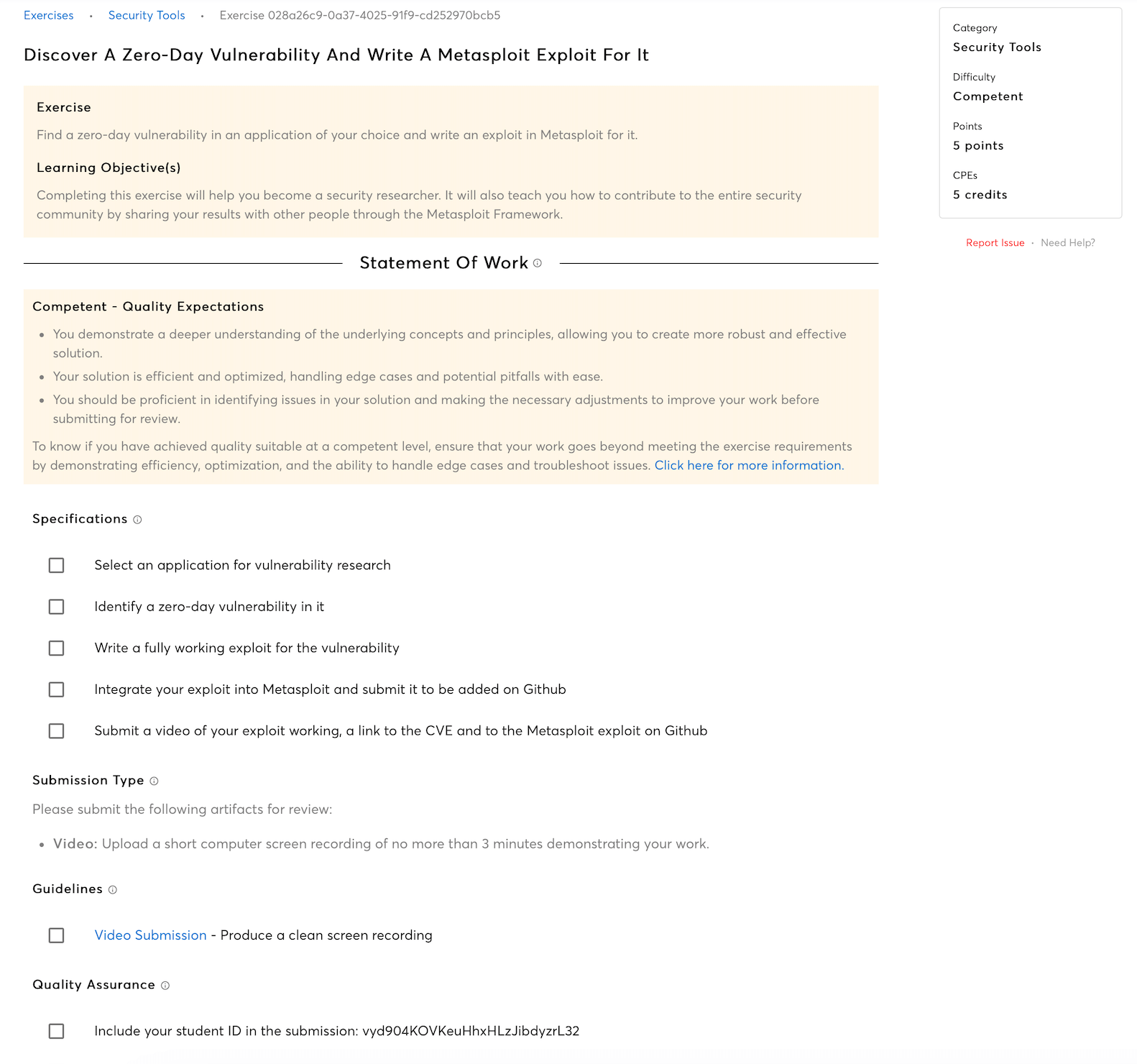
Executing Sophisticated Exploitation Techniques
Learn to execute sophisticated exploitation techniques to uncover vulnerabilities in operating systems, leveraging Metasploit's extensive capabilities to identify and exploit security weaknesses effectively.
Harnessing Metasploit for Targeted Attacks
Harness Metasploit's capabilities to launch targeted attacks and assess system vulnerabilities, utilizing its powerful features to simulate real-world cyber threats and evaluate security defenses.
Generating Comprehensive Security Reports
Master the art of generating comprehensive reports detailing security findings and recommendations, utilizing Metasploit's reporting functionalities to communicate vulnerabilities and mitigation strategies effectively to stakeholders.
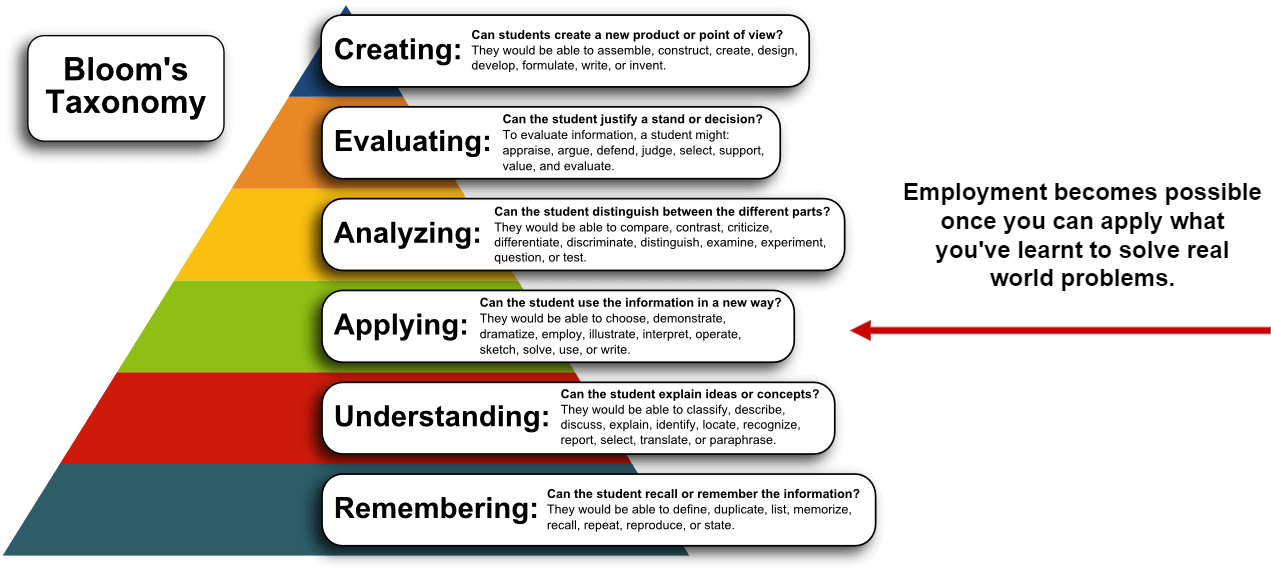
By the end of this comprehensive bootcamp, you'll emerge as a proficient Metasploit user, equipped with the knowledge and skills needed to navigate the ever-evolving landscape of cybersecurity with confidence. With this expertise, you'll be empowered to conduct thorough vulnerability assessments, penetration tests, and security analyses. Whether you aim to enhance your current role, explore new career opportunities, or bolster your cybersecurity capabilities as an independent professional, this bootcamp will equip you with the tools and know-how to excel in various cybersecurity endeavors.
Training Modules
This course provides you with multiple training modules, each of which is designed to teach you practical skills that can help you solve important cyber problems. Each module offers exercises that will help you build your skills and capabilities.
-
MM-01:
Initial Access
- 6 exercises
-
MM-02:
Collection
- 5 exercises
-
MM-03:
Compromising Credentials
- 5 exercises
-
MM-04:
Defense Evasion
- 5 exercises
-
MM-05:
Lateral Movement and Persistence
- 4 exercises
-
MM-06:
Advanced Capabilities
- 4 exercises
Certificate of Completion
You will receive a Certificate of Completion when you complete this course.
A Certificate of Completion can be very beneficial, especially when job hunting. It proves that you have completed a course and can be a great way to stand out among other candidates. Even if you do not have much experience, it shows that you are willing to learn and have the basic skills required for the job. In addition, some employers may require a Certificate of Completion for certain positions. Therefore, adding it to your portfolio is always an excellent choice.

 Beginner
Beginner